- Welcome to AHXproject.
AHXproject
< | >
Recent posts
#81
9to5Linux / Sigil 2.7.5 Open-Source EPUB ...
Last post by tim - Mar 13, 2026, 06:09 PMSigil 2.7.5 Open-Source EPUB Ebook Editor Is Out with New Features and Bug Fixes

Sigil 2.7.5 open-source and cross-platform EPUB ebook editor is now available for download with various new features and bug fixes. Here's what's new!
The post Sigil 2.7.5 Open-Source EPUB Ebook Editor Is Out with New Features and Bug Fixes appeared first on 9to5Linux - do not reproduce this article without permission. This RSS feed is intended for readers, not scrapers.
Categories: Apps, News, ebook editor, EPUB editor, Sigil
Source: https://9to5linux.com/sigil-2-7-5-open-source-epub-ebook-editor-is-out-with-new-features-and-bug-fixes Mar 11, 2026, 08:56 PM

Sigil 2.7.5 open-source and cross-platform EPUB ebook editor is now available for download with various new features and bug fixes. Here's what's new!
The post Sigil 2.7.5 Open-Source EPUB Ebook Editor Is Out with New Features and Bug Fixes appeared first on 9to5Linux - do not reproduce this article without permission. This RSS feed is intended for readers, not scrapers.
Categories: Apps, News, ebook editor, EPUB editor, Sigil
Source: https://9to5linux.com/sigil-2-7-5-open-source-epub-ebook-editor-is-out-with-new-features-and-bug-fixes Mar 11, 2026, 08:56 PM
#82
9to5Linux / Calamares Linux Graphical Ins...
Last post by tim - Mar 13, 2026, 06:09 PMCalamares Linux Graphical Installer Now Supports KDE's Plasma Login Manager

Calamares 3.4.2 open-source universal graphical installer for GNU/Linux distributions is now available for download with support for Plasma Login Manager. Here's what's new!
The post Calamares Linux Graphical Installer Now Supports KDE's Plasma Login Manager appeared first on 9to5Linux - do not reproduce this article without permission. This RSS feed is intended for readers, not scrapers.
Categories: Apps, News, Calamares, Calamares installer, graphical installer, Linux installer
Source: https://9to5linux.com/calamares-linux-graphical-installer-now-supports-kdes-plasma-login-manager Mar 10, 2026, 08:50 PM

Calamares 3.4.2 open-source universal graphical installer for GNU/Linux distributions is now available for download with support for Plasma Login Manager. Here's what's new!
The post Calamares Linux Graphical Installer Now Supports KDE's Plasma Login Manager appeared first on 9to5Linux - do not reproduce this article without permission. This RSS feed is intended for readers, not scrapers.
Categories: Apps, News, Calamares, Calamares installer, graphical installer, Linux installer
Source: https://9to5linux.com/calamares-linux-graphical-installer-now-supports-kdes-plasma-login-manager Mar 10, 2026, 08:50 PM
#83
9to5Linux / NVIDIA 580.142 Production-Rea...
Last post by tim - Mar 13, 2026, 06:09 PMNVIDIA 580.142 Production-Ready Linux Graphics Driver Released with Bug Fixes
NVIDIA 580.142 production-ready graphics driver for Linux is now available for download with various bug fixes to improve stability.
The post NVIDIA 580.142 Production-Ready Linux Graphics Driver Released with Bug Fixes appeared first on 9to5Linux - do not reproduce this article without permission. This RSS feed is intended for readers, not scrapers.
Categories: Drivers, News, graphics driver, Nvidia, video driver
Source: https://9to5linux.com/nvidia-580-142-production-ready-linux-graphics-driver-released-with-bug-fixes Mar 10, 2026, 07:57 PM
NVIDIA 580.142 production-ready graphics driver for Linux is now available for download with various bug fixes to improve stability.
The post NVIDIA 580.142 Production-Ready Linux Graphics Driver Released with Bug Fixes appeared first on 9to5Linux - do not reproduce this article without permission. This RSS feed is intended for readers, not scrapers.
Categories: Drivers, News, graphics driver, Nvidia, video driver
Source: https://9to5linux.com/nvidia-580-142-production-ready-linux-graphics-driver-released-with-bug-fixes Mar 10, 2026, 07:57 PM
#84
9to5Linux / OpenSSL 4.0 Promises Support ...
Last post by tim - Mar 13, 2026, 06:09 PMOpenSSL 4.0 Promises Support for Encrypted Client Hello, SNMP KDF, and SRTP KDF
OpenSSL 4.0 is now available for public testing with an alpha version adding support for Encrypted Client Hello, support for SNMP KDF and SRTP KDF, and other changes. Here's what to expect!
The post OpenSSL 4.0 Promises Support for Encrypted Client Hello, SNMP KDF, and SRTP KDF appeared first on 9to5Linux - do not reproduce this article without permission. This RSS feed is intended for readers, not scrapers.
Categories: Apps, News, OpenSSL
Source: https://9to5linux.com/openssl-4-0-promises-support-for-encrypted-client-hello-snmp-kdf-and-srtp-kdf Mar 10, 2026, 05:36 PM
OpenSSL 4.0 is now available for public testing with an alpha version adding support for Encrypted Client Hello, support for SNMP KDF and SRTP KDF, and other changes. Here's what to expect!
The post OpenSSL 4.0 Promises Support for Encrypted Client Hello, SNMP KDF, and SRTP KDF appeared first on 9to5Linux - do not reproduce this article without permission. This RSS feed is intended for readers, not scrapers.
Categories: Apps, News, OpenSSL
Source: https://9to5linux.com/openssl-4-0-promises-support-for-encrypted-client-hello-snmp-kdf-and-srtp-kdf Mar 10, 2026, 05:36 PM
#85
Ubuntu Blog / AppArmor vulnerability fixes ...
Last post by tim - Mar 13, 2026, 06:09 PMAppArmor vulnerability fixes available
Qualys discovered several vulnerabilities in the AppArmor code of the Linux kernel. These are being referred to as CrackArmor, while CVE IDs have not been assigned yet. All of the vulnerabilities require unprivileged local user access. The impact of these vulnerabilities ranges from denial of service to kernel memory information leak, removing security controls, and local privilege escalation to root user. Ubuntu releases are affected differently and this is detailed in the corresponding sections below.
Linux kernel fixes for the supported Ubuntu releases are being made available as security updates by the Canonical Kernel Team. Furthermore, our security team has provided userspace mitigations in the form of security updates, for all affected Ubuntu releases. Our recommendation is that you apply both userspace mitigations and Linux kernel security updates.
AppArmor is a Mandatory Access Control (MAC) Linux Security Module that provides an additional layer of security on Ubuntu systems and supplements the traditional Discretionary Access Control (DAC) model. In addition to being enabled by default on Ubuntu releases, AppArmor is also used by other Linux distributions.
Vulnerability summary
This blog provides a summary of the reported security vulnerabilities in the AppArmor Linux kernel code and the sudo application, as well as unsafe behaviour in the su utility which facilitates exploitation of the AppArmor kernel vulnerabilities. The following table summarizes the issues:
PackageDescriptionCVE IDslinuxAll of the AppArmor vulnerabilities are in the Linux kernel. On host deployments, these rely on a fundamental "confused deputy" issue for exploitation, which is one of the AppArmor vulnerabilities.Security updates are available for some affected releases.No CVE assigned yet. These are referred to as CrackArmor. Tracked as Launchpad Bug #2143853 sudosudo-ldapThe sudo utility has a vulnerability that can lead to local privilege escalation in host deployment scenarios, when combined with other vulnerabilities described here.Security updates are available for all affected releases.No CVE assigned, tracked as Launchpad Bug #2143042 util-linuxThe su utility in the util-linux package exhibits unsafe behaviour which facilitates the exploitation of the AppArmor vulnerabilities in host deployment scenarios.Security updates which harden the su utility are available for all affected releases.This is not a vulnerability, so it will not receive a CVE identifier. Tracked as Launchpad Bug #2143850 AppArmor vulnerability summary
The Vulnerability Knowledge Base article contains a detailed description of the vulnerabilities, as well as of the mitigations provided via security updates.
Impact scenarios/assessment
Deployments without container workloads
Exploitation on hosts not running container workloads requires the cooperation of a privileged application (e.g. a setuid binary). The presence of a container orchestration system without running containers does not by itself create an exploitation opportunity. The Qualys team have identified the behaviour of the su utility as enabling exploitation. This can only be triggered by unprivileged users that have a password set – unprivileged system users cannot invoke su successfully without having access to an account's password and hence cannot trigger the vulnerabilities. In the absence of such a cooperating privileged application, the vulnerabilities can only be triggered by a privileged user (root).
An unrelated vulnerability has been identified by Qualys in sudo which can be triggered through the email notifications feature. This vulnerability enables local privilege escalation when chained with the AppArmor vulnerabilities and the su privileged application. sudo-rs, the Rust-rewrite of sudo available by default in Ubuntu Questing Quokka (25.10) and later, is not affected because of the design decision to not send email notifications.
The Ubuntu Security Team has prepared security updates for both su (in the util-linux package) and sudo. The su security patch should be considered a mitigation and we strongly recommend that you additionally apply the Linux kernel security updates as soon as possible.
Container deployments
In container deployments that may execute potentially-malicious attacker-controlled container images, the AppArmor Linux kernel vulnerabilities can be exploited without the need for a cooperating privileged userspace application. This could theoretically enable container escape scenarios, although this has not been practically demonstrated at the time of writing.
The Ubuntu Security Team strongly recommends applying the Linux kernel security updates as the only available remediation.
The following sections explain how different Ubuntu releases are impacted, and associated fixes or mitigations.
Linux kernel security updates
The Linux kernel security updates address all of the AppArmor vulnerabilities identified by Qualys.
All supported Ubuntu releases are affected by the fundamental "confused deputy" vulnerability. The combination of vulnerabilities that enable local privilege escalation and container escape scenarios is not present in Trusty Tahr (14.04 LTS) or Xenial Xerus (16.04 LTS).
How to check if you are impacted
On your system, run the following command to get the version of the currently running kernel and compare the listed version to the corresponding table below.
uname -r
The list of installed kernel packages can be obtained using the following command:
dpkg -l 'linux-image*' | grep ^ii
You can compare the version of the specific kernel variant that you have installed against the per-release version table available in the Vulnerability Knowledge Base article .
How to address
Please note that the Linux kernel images are currently in the process of being made available in the Ubuntu Archive. When they are released, we recommend you upgrade all packages:
sudo apt update && sudo apt upgrade
If this is not possible and the Linux kernel is installed via a meta package, its update can be targeted directly:
sudo apt update
dpkg-query -W -f '${source:Package}\t${binary:Package}\n' | awk '$1 ~ "^linux-meta" { print $2 }' | xargs sudo apt install --only-upgrade
Once the security updates for the Linux kernel are installed, a reboot is required:
sudo reboot
The unattended-upgrades feature is enabled by default for Ubuntu Xenial Xerus (16.04 LTS) onwards. This service:
The sudo package security updates address the unrelated sudo vulnerability that can be chained with the AppArmor vulnerability to facilitate local privilege escalation.
How to check if you are impacted
To get the version of the sudo package installed, run the following command:
dpkg -l 'sudo*' | grep ^ii
The following table lists the fixed versions of the sudo package in all supported Ubuntu releases:
ReleasePackageFixed versionQuesting Quokka (25.10)sudo1.9.17p2-1ubuntu1.1sudo-ldap1.9.17p2-1ubuntu1.1sudo-rsNot affectedNoble Numbat (24.04 LTS)sudo1.9.15p5-3ubuntu5.24.04.2sudo-ldap1.9.15p5-3ubuntu5.24.04.2Jammy Jellyfish (22.04 LTS)sudo1.9.9-1ubuntu2.6sudo-ldap1.9.9-1ubuntu2.6Focal Fossa (20.04 LTS)sudoNot affectedsudo-ldapNot affectedBionic Beaver (18.04 LTS)sudoNot affectedsudo-ldapNot affectedXenial Xerus (16.05 LTS)sudoNot affectedsudo-ldapNot affectedTrusty Tahr (14.04 LTS)sudoNot affectedsudo-ldapNot affectedAffected sudo versions
How to address
We recommend you upgrade all packages:
sudo apt update && sudo apt upgrade
If this is not possible, the sudo userspace mitigations can be installed directly and does not require a reboot to apply:
sudo apt update
sudo apt install sudo
The unattended-upgrades feature is enabled by default for Ubuntu Xenial Xerus (16.04 LTS) onwards. This service:
The util-linux package security updates harden the su utility to avoid it being used to exploit the AppArmor vulnerabilities.
How to check if you are impacted
To get the version of the util-linux package installed, run the following command:
dpkg -l util-linux
The following table lists the fixed versions of the sudo package in all supported Ubuntu releases:
ReleasePackageFixed versionQuesting Quokka (25.10)util-linux2.41-4ubuntu4.2Noble Numbat (24.04 LTS)util-linux2.39.3-9ubuntu6.5Jammy Jellyfish (22.04 LTS)util-linux2.37.2-4ubuntu3.5Focal Fossa (20.04 LTS)util-linux2.34-0.1ubuntu9.6+esm1Bionic Beaver (18.04 LTS)util-linuxNot affectedXenial Xerus (16.05 LTS)util-linuxNot affectedTrusty Tahr (14.04 LTS)util-linuxNot affectedAffected util-linux versions
How to address
We recommend you upgrade all packages:
sudo apt update && sudo apt upgrade
If this is not possible, the util-linux userspace mitigations can be installed directly and does not require a reboot to apply:
sudo apt update
sudo apt install util-linux
The unattended-upgrades feature is enabled by default for Ubuntu Xenial Xerus (16.04 LTS) onwards. This service:
We would like to thank Qualys for their excellent reporting and for engaging with the AppArmor team, the Canonical Kernel Team, the Ubuntu Security Team, the Linux Kernel Security Team, and other Linux distributions in coordinated vulnerability disclosure.
References
Ubuntu Vulnerability Knowledge Base Article Qualys CrackArmor security advisory
Qualys discovered several vulnerabilities in the AppArmor code of the Linux kernel. These are being referred to as CrackArmor, while CVE IDs have not been assigned yet. All of the vulnerabilities require unprivileged local user access. The impact of these vulnerabilities ranges from denial of service to kernel memory information leak, removing security controls, and [...]
Categories: Security, Vulnerabilities
Source: https://ubuntu.com//blog/apparmor-vulnerability-fixes-available Mar 13, 2026, 01:46 AM
Qualys discovered several vulnerabilities in the AppArmor code of the Linux kernel. These are being referred to as CrackArmor, while CVE IDs have not been assigned yet. All of the vulnerabilities require unprivileged local user access. The impact of these vulnerabilities ranges from denial of service to kernel memory information leak, removing security controls, and local privilege escalation to root user. Ubuntu releases are affected differently and this is detailed in the corresponding sections below.
Linux kernel fixes for the supported Ubuntu releases are being made available as security updates by the Canonical Kernel Team. Furthermore, our security team has provided userspace mitigations in the form of security updates, for all affected Ubuntu releases. Our recommendation is that you apply both userspace mitigations and Linux kernel security updates.
AppArmor is a Mandatory Access Control (MAC) Linux Security Module that provides an additional layer of security on Ubuntu systems and supplements the traditional Discretionary Access Control (DAC) model. In addition to being enabled by default on Ubuntu releases, AppArmor is also used by other Linux distributions.
Vulnerability summary
This blog provides a summary of the reported security vulnerabilities in the AppArmor Linux kernel code and the sudo application, as well as unsafe behaviour in the su utility which facilitates exploitation of the AppArmor kernel vulnerabilities. The following table summarizes the issues:
PackageDescriptionCVE IDslinuxAll of the AppArmor vulnerabilities are in the Linux kernel. On host deployments, these rely on a fundamental "confused deputy" issue for exploitation, which is one of the AppArmor vulnerabilities.Security updates are available for some affected releases.No CVE assigned yet. These are referred to as CrackArmor. Tracked as Launchpad Bug #2143853 sudosudo-ldapThe sudo utility has a vulnerability that can lead to local privilege escalation in host deployment scenarios, when combined with other vulnerabilities described here.Security updates are available for all affected releases.No CVE assigned, tracked as Launchpad Bug #2143042 util-linuxThe su utility in the util-linux package exhibits unsafe behaviour which facilitates the exploitation of the AppArmor vulnerabilities in host deployment scenarios.Security updates which harden the su utility are available for all affected releases.This is not a vulnerability, so it will not receive a CVE identifier. Tracked as Launchpad Bug #2143850 AppArmor vulnerability summary
The Vulnerability Knowledge Base article contains a detailed description of the vulnerabilities, as well as of the mitigations provided via security updates.
Impact scenarios/assessment
Deployments without container workloads
Exploitation on hosts not running container workloads requires the cooperation of a privileged application (e.g. a setuid binary). The presence of a container orchestration system without running containers does not by itself create an exploitation opportunity. The Qualys team have identified the behaviour of the su utility as enabling exploitation. This can only be triggered by unprivileged users that have a password set – unprivileged system users cannot invoke su successfully without having access to an account's password and hence cannot trigger the vulnerabilities. In the absence of such a cooperating privileged application, the vulnerabilities can only be triggered by a privileged user (root).
An unrelated vulnerability has been identified by Qualys in sudo which can be triggered through the email notifications feature. This vulnerability enables local privilege escalation when chained with the AppArmor vulnerabilities and the su privileged application. sudo-rs, the Rust-rewrite of sudo available by default in Ubuntu Questing Quokka (25.10) and later, is not affected because of the design decision to not send email notifications.
The Ubuntu Security Team has prepared security updates for both su (in the util-linux package) and sudo. The su security patch should be considered a mitigation and we strongly recommend that you additionally apply the Linux kernel security updates as soon as possible.
Container deployments
In container deployments that may execute potentially-malicious attacker-controlled container images, the AppArmor Linux kernel vulnerabilities can be exploited without the need for a cooperating privileged userspace application. This could theoretically enable container escape scenarios, although this has not been practically demonstrated at the time of writing.
The Ubuntu Security Team strongly recommends applying the Linux kernel security updates as the only available remediation.
The following sections explain how different Ubuntu releases are impacted, and associated fixes or mitigations.
Linux kernel security updates
The Linux kernel security updates address all of the AppArmor vulnerabilities identified by Qualys.
All supported Ubuntu releases are affected by the fundamental "confused deputy" vulnerability. The combination of vulnerabilities that enable local privilege escalation and container escape scenarios is not present in Trusty Tahr (14.04 LTS) or Xenial Xerus (16.04 LTS).
How to check if you are impacted
On your system, run the following command to get the version of the currently running kernel and compare the listed version to the corresponding table below.
uname -r
The list of installed kernel packages can be obtained using the following command:
dpkg -l 'linux-image*' | grep ^ii
You can compare the version of the specific kernel variant that you have installed against the per-release version table available in the Vulnerability Knowledge Base article .
How to address
Please note that the Linux kernel images are currently in the process of being made available in the Ubuntu Archive. When they are released, we recommend you upgrade all packages:
sudo apt update && sudo apt upgrade
If this is not possible and the Linux kernel is installed via a meta package, its update can be targeted directly:
sudo apt update
dpkg-query -W -f '${source:Package}\t${binary:Package}\n' | awk '$1 ~ "^linux-meta" { print $2 }' | xargs sudo apt install --only-upgrade
Once the security updates for the Linux kernel are installed, a reboot is required:
sudo reboot
The unattended-upgrades feature is enabled by default for Ubuntu Xenial Xerus (16.04 LTS) onwards. This service:
- Applies new security updates every 24 hours automatically.
- If you have this enabled, the patches above will be automatically applied within 24 hours of being available, but a reboot will still be required.
The sudo package security updates address the unrelated sudo vulnerability that can be chained with the AppArmor vulnerability to facilitate local privilege escalation.
How to check if you are impacted
To get the version of the sudo package installed, run the following command:
dpkg -l 'sudo*' | grep ^ii
The following table lists the fixed versions of the sudo package in all supported Ubuntu releases:
ReleasePackageFixed versionQuesting Quokka (25.10)sudo1.9.17p2-1ubuntu1.1sudo-ldap1.9.17p2-1ubuntu1.1sudo-rsNot affectedNoble Numbat (24.04 LTS)sudo1.9.15p5-3ubuntu5.24.04.2sudo-ldap1.9.15p5-3ubuntu5.24.04.2Jammy Jellyfish (22.04 LTS)sudo1.9.9-1ubuntu2.6sudo-ldap1.9.9-1ubuntu2.6Focal Fossa (20.04 LTS)sudoNot affectedsudo-ldapNot affectedBionic Beaver (18.04 LTS)sudoNot affectedsudo-ldapNot affectedXenial Xerus (16.05 LTS)sudoNot affectedsudo-ldapNot affectedTrusty Tahr (14.04 LTS)sudoNot affectedsudo-ldapNot affectedAffected sudo versions
How to address
We recommend you upgrade all packages:
sudo apt update && sudo apt upgrade
If this is not possible, the sudo userspace mitigations can be installed directly and does not require a reboot to apply:
sudo apt update
sudo apt install sudo
The unattended-upgrades feature is enabled by default for Ubuntu Xenial Xerus (16.04 LTS) onwards. This service:
- Applies new security updates every 24 hours automatically.
- If you have this enabled, the patches above will be automatically applied within 24 hours of being available.
The util-linux package security updates harden the su utility to avoid it being used to exploit the AppArmor vulnerabilities.
How to check if you are impacted
To get the version of the util-linux package installed, run the following command:
dpkg -l util-linux
The following table lists the fixed versions of the sudo package in all supported Ubuntu releases:
ReleasePackageFixed versionQuesting Quokka (25.10)util-linux2.41-4ubuntu4.2Noble Numbat (24.04 LTS)util-linux2.39.3-9ubuntu6.5Jammy Jellyfish (22.04 LTS)util-linux2.37.2-4ubuntu3.5Focal Fossa (20.04 LTS)util-linux2.34-0.1ubuntu9.6+esm1Bionic Beaver (18.04 LTS)util-linuxNot affectedXenial Xerus (16.05 LTS)util-linuxNot affectedTrusty Tahr (14.04 LTS)util-linuxNot affectedAffected util-linux versions
How to address
We recommend you upgrade all packages:
sudo apt update && sudo apt upgrade
If this is not possible, the util-linux userspace mitigations can be installed directly and does not require a reboot to apply:
sudo apt update
sudo apt install util-linux
The unattended-upgrades feature is enabled by default for Ubuntu Xenial Xerus (16.04 LTS) onwards. This service:
- Applies new security updates every 24 hours automatically.
- If you have this enabled, the patches above will be automatically applied within 24 hours of being available.
We would like to thank Qualys for their excellent reporting and for engaging with the AppArmor team, the Canonical Kernel Team, the Ubuntu Security Team, the Linux Kernel Security Team, and other Linux distributions in coordinated vulnerability disclosure.
References
Ubuntu Vulnerability Knowledge Base Article Qualys CrackArmor security advisory
Qualys discovered several vulnerabilities in the AppArmor code of the Linux kernel. These are being referred to as CrackArmor, while CVE IDs have not been assigned yet. All of the vulnerabilities require unprivileged local user access. The impact of these vulnerabilities ranges from denial of service to kernel memory information leak, removing security controls, and [...]
Categories: Security, Vulnerabilities
Source: https://ubuntu.com//blog/apparmor-vulnerability-fixes-available Mar 13, 2026, 01:46 AM
#86
Ubuntu Blog / The bare metal problem in AI ...
Last post by tim - Mar 13, 2026, 06:09 PMThe bare metal problem in AI Factories
Operational challenges in modern AI infrastructure
As AI platforms grow in scale, many of the limiting factors are no longer related to model design or algorithmic performance, but to the operation of the underlying infrastructure. GPU accelerators are key components and are responsible for a large part of the total system cost, which makes their continuous availability and stable operation critical to the output and efficiency of the entire AI platform. However, hardware failures, driver issues, and configuration problems happen periodically, bringing down the usable capacity.
These challenges become more visible in large, continuously operating environments, such as AI Factories, where infrastructure is expected to run at high utilization over long periods of time. In such deployments, even short disruptions at the hardware level translate directly into lost throughput and reduced return on investment. As a result, the reliability and manageability of the physical infrastructure have become central concerns in the design and operation of modern AI systems. In this article, we'll explore why bare metal automation has become so critical for AI infrastructure, and highlight how Canonical MAAS can be a solution for AI Factories.
AI Factories: cloud-native software, bare metal hardware
AI Factories are large-scale AI environments designed to operate continuously, converting data and compute capacity into models, predictions, or generated content. They are typically built to maximize throughput from expensive accelerator hardware and to support a steady flow of training and inference workloads. The term is relatively new, and it describes a class of deployments where efficiency, repeatability, and sustained utilization are primary design goals.
From an architectural perspective, AI Factories are cloud-native at the software layer. Workloads are commonly containerized and orchestrated using Kubernetes, which provides scheduling, isolation, and automation for AI jobs. At the same time, these environments often rely on direct access to physical servers to meet performance requirements. Virtualization is frequently avoided in order to preserve low latency, full GPU access, and high-speed networking. The result is a layered architecture in which cloud-native software depends on a bare metal foundation that must be stable, consistent, and efficiently managed.
The role of bare metal automation in AI infrastructure
In these GPU-dense AI environments, hardware and low-level software issues are not exceptional events but expected operational conditions. Hardware failures, driver incompatibilities, kernel-level errors, and configuration drift occur regularly at scale and result in unusable machines, usually for extended periods of time. If recovery and reprovisioning depend on manual intervention, these failures lead directly to long downtime and reduced hardware capacity – so this is where bare metal automation comes in.
Bare metal automation refers to the automated provisioning, configuration, and lifecycle management of physical servers. This includes operating system deployment, configuration, and hardware validation. It enables infrastructure teams to keep a consistent and healthy inventory, reprovision nodes easily, and recover from hardware or system-level failures with minimal manual intervention. With bare metal automation, organizations can treat physical servers as flexible resources, limiting the operational impact of hardware faults and maintaining a higher level of effective capacity across the AI platform.
Canonical MAAS as a foundation for AI Factories operations
Bare metal as cloud-like resources
Canonical MAAS provides a way to manage bare metal infrastructure with the same expectations of automation and elasticity commonly associated with cloud platforms. It turns physical servers into programmable resources that can be provisioned, reconfigured, and redeployed through automated workflows, rather than manual processes. The support for Infrastructure as Code tools, such as Terraform provides a complete integration with the rest of the AI infrastructure.
This flexibility is particularly well suited to AI environments, where hardware must be brought online quickly, recovered reliably after failures, and reassigned as workload requirements change.
Predictable lifecycle management
The nodes are constantly accessible from MAAS through the board management controller (BMC), which provides an out-of-band channel that enables MAAS to control the power and the full lifecycle of the nodes:
MAAS communicates with the nodes through the board management controller (BMC), which manages the full lifecycle of the machines, enabling automated provisioning, recovery, and recycling of servers, and allowing failed or misconfigured nodes to be returned to service with minimal delay.
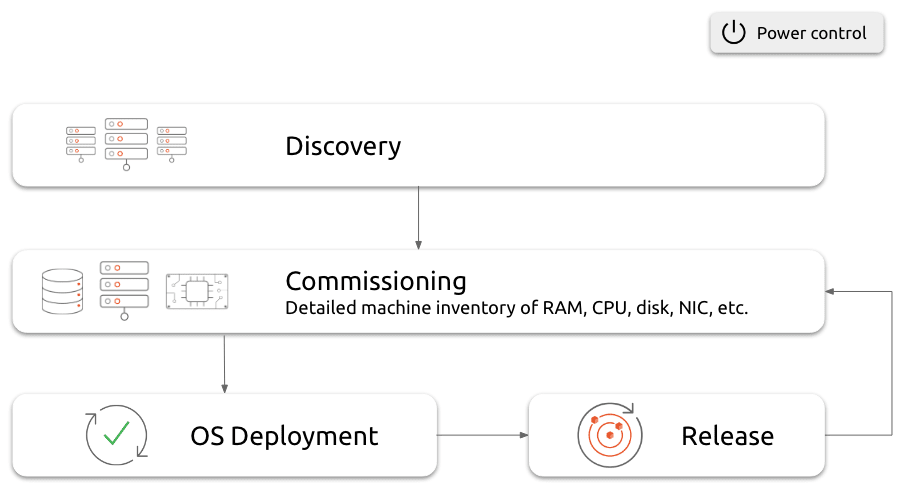 Server lifecycle management with MAAS
Server lifecycle management with MAAS
A critical aspect of this model is hardware validation and health management. MAAS supports hardware testing as part of the process, allowing systems to be verified before they are placed into production. This reduces the risk of introducing faulty components into active AI clusters. In addition, regular testing and hardware health monitoring help detect degradation or latent failures over time, enabling proactive maintenance rather than reactive recovery.
All these capabilities help ensure that the physical layer remains stable and predictable.
The foundation for bare metal Kubernetes
As a bare metal cloud provider, MAAS can serve as a physical cloud below Kubernetes . It complements workload orchestration by ensuring that the underlying hardware remains available and consistent. MAAS is fully integrated with Juju . This combination provides full system orchestration, enabling coordinated management of the physical machines and workloads.
Infrastructure operations and return on investment
There are many factors that impact the efficiency of an AI infrastructure. Scheduling and workload management influence performance, but hardware availability is mainly driven by infrastructure operations. So the overall output of an AI platform depends on the stable availability of hardware and perfect coordination with the workload management. Slow provisioning, inconsistent configurations, and long recovery processes reduce effective capacity and increase the cost per unit of AI output.
By automating bare metal provisioning and lifecycle management, infrastructure teams can reduce downtime, improve consistency, and keep more accelerators in productive use. In this way, improvements in infrastructure operations translate directly into higher utilization and better return on investment.
For organizations that operate large AI platforms, including AI Factories, bare metal automation is a key factor in the economic performance of the system. Kubernetes provides workload orchestration, but automated bare metal management determines how reliably AI infrastructure can deliver value.
Further reading and next steps
In order to explore these topics in more detail, the following resources provide additional background and practical guidance:
Or reach out to our team of experts if you want to learn more about how to get full MAAS support.
As AI platforms grow into large-scale "AI Factories," the real bottleneck shifts from model design to operational complexity. With expensive GPU accelerators, hardware failures and inconsistent configurations lead directly to lost throughput and reduced return on investment. While Kubernetes orchestrates workloads, it cannot fix broken physical infrastructure. This is why bare metal automation is now a first-order AI performance lever. Canonical MAAS is the foundational solution, turning physical servers into programmable, cloud-like resources that can be provisioned, recovered, and repurposed efficiently, ensuring higher utilization and a better ROI for your AI infrastructure.
Categories: AI, AI Factory, bare metal, bare metal kubernetes, MAAS
Source: https://ubuntu.com//blog/the-bare-metal-problem-in-ai-factories Mar 11, 2026, 11:43 PM
Operational challenges in modern AI infrastructure
As AI platforms grow in scale, many of the limiting factors are no longer related to model design or algorithmic performance, but to the operation of the underlying infrastructure. GPU accelerators are key components and are responsible for a large part of the total system cost, which makes their continuous availability and stable operation critical to the output and efficiency of the entire AI platform. However, hardware failures, driver issues, and configuration problems happen periodically, bringing down the usable capacity.
These challenges become more visible in large, continuously operating environments, such as AI Factories, where infrastructure is expected to run at high utilization over long periods of time. In such deployments, even short disruptions at the hardware level translate directly into lost throughput and reduced return on investment. As a result, the reliability and manageability of the physical infrastructure have become central concerns in the design and operation of modern AI systems. In this article, we'll explore why bare metal automation has become so critical for AI infrastructure, and highlight how Canonical MAAS can be a solution for AI Factories.
AI Factories: cloud-native software, bare metal hardware
AI Factories are large-scale AI environments designed to operate continuously, converting data and compute capacity into models, predictions, or generated content. They are typically built to maximize throughput from expensive accelerator hardware and to support a steady flow of training and inference workloads. The term is relatively new, and it describes a class of deployments where efficiency, repeatability, and sustained utilization are primary design goals.
From an architectural perspective, AI Factories are cloud-native at the software layer. Workloads are commonly containerized and orchestrated using Kubernetes, which provides scheduling, isolation, and automation for AI jobs. At the same time, these environments often rely on direct access to physical servers to meet performance requirements. Virtualization is frequently avoided in order to preserve low latency, full GPU access, and high-speed networking. The result is a layered architecture in which cloud-native software depends on a bare metal foundation that must be stable, consistent, and efficiently managed.
The role of bare metal automation in AI infrastructure
In these GPU-dense AI environments, hardware and low-level software issues are not exceptional events but expected operational conditions. Hardware failures, driver incompatibilities, kernel-level errors, and configuration drift occur regularly at scale and result in unusable machines, usually for extended periods of time. If recovery and reprovisioning depend on manual intervention, these failures lead directly to long downtime and reduced hardware capacity – so this is where bare metal automation comes in.
Bare metal automation refers to the automated provisioning, configuration, and lifecycle management of physical servers. This includes operating system deployment, configuration, and hardware validation. It enables infrastructure teams to keep a consistent and healthy inventory, reprovision nodes easily, and recover from hardware or system-level failures with minimal manual intervention. With bare metal automation, organizations can treat physical servers as flexible resources, limiting the operational impact of hardware faults and maintaining a higher level of effective capacity across the AI platform.
Canonical MAAS as a foundation for AI Factories operations
Bare metal as cloud-like resources
Canonical MAAS provides a way to manage bare metal infrastructure with the same expectations of automation and elasticity commonly associated with cloud platforms. It turns physical servers into programmable resources that can be provisioned, reconfigured, and redeployed through automated workflows, rather than manual processes. The support for Infrastructure as Code tools, such as Terraform provides a complete integration with the rest of the AI infrastructure.
This flexibility is particularly well suited to AI environments, where hardware must be brought online quickly, recovered reliably after failures, and reassigned as workload requirements change.
Predictable lifecycle management
The nodes are constantly accessible from MAAS through the board management controller (BMC), which provides an out-of-band channel that enables MAAS to control the power and the full lifecycle of the nodes:
- Discovery: New machines are discovered and added to the inventory
- Commissioning: Detect the hardware capabilities of the machines (CPU, memory, network interfaces, disks, etc.)
- Deployment: Deploy the operating system using PXE boot on the machine
- Repurposing: Release the machine so that it can be reused
MAAS communicates with the nodes through the board management controller (BMC), which manages the full lifecycle of the machines, enabling automated provisioning, recovery, and recycling of servers, and allowing failed or misconfigured nodes to be returned to service with minimal delay.
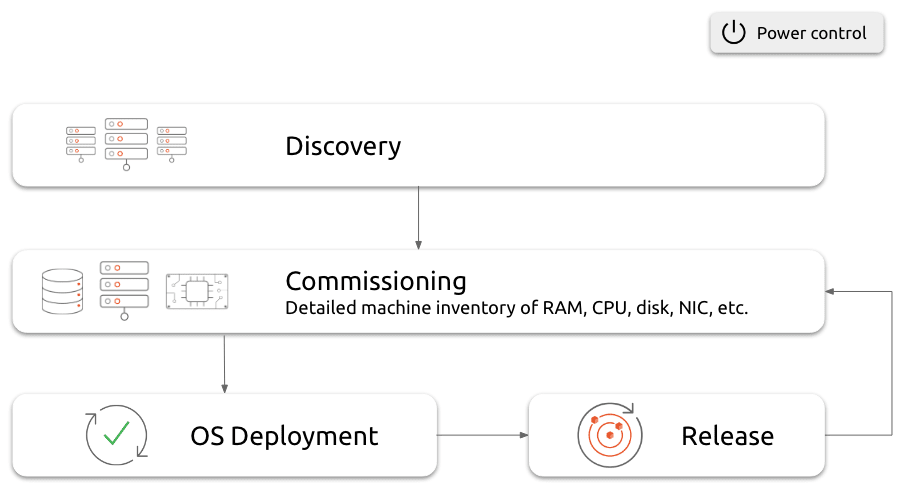 Server lifecycle management with MAAS
Server lifecycle management with MAASA critical aspect of this model is hardware validation and health management. MAAS supports hardware testing as part of the process, allowing systems to be verified before they are placed into production. This reduces the risk of introducing faulty components into active AI clusters. In addition, regular testing and hardware health monitoring help detect degradation or latent failures over time, enabling proactive maintenance rather than reactive recovery.
All these capabilities help ensure that the physical layer remains stable and predictable.
The foundation for bare metal Kubernetes
As a bare metal cloud provider, MAAS can serve as a physical cloud below Kubernetes . It complements workload orchestration by ensuring that the underlying hardware remains available and consistent. MAAS is fully integrated with Juju . This combination provides full system orchestration, enabling coordinated management of the physical machines and workloads.
Infrastructure operations and return on investment
There are many factors that impact the efficiency of an AI infrastructure. Scheduling and workload management influence performance, but hardware availability is mainly driven by infrastructure operations. So the overall output of an AI platform depends on the stable availability of hardware and perfect coordination with the workload management. Slow provisioning, inconsistent configurations, and long recovery processes reduce effective capacity and increase the cost per unit of AI output.
By automating bare metal provisioning and lifecycle management, infrastructure teams can reduce downtime, improve consistency, and keep more accelerators in productive use. In this way, improvements in infrastructure operations translate directly into higher utilization and better return on investment.
For organizations that operate large AI platforms, including AI Factories, bare metal automation is a key factor in the economic performance of the system. Kubernetes provides workload orchestration, but automated bare metal management determines how reliably AI infrastructure can deliver value.
Further reading and next steps
In order to explore these topics in more detail, the following resources provide additional background and practical guidance:
- An overview of how Canonical MAAS enables automated provisioning, hardware testing, and lifecycle management for bare metal infrastructure.
- Guidance on for full-stack infrastructure and platform orchestration.
- The comprehensive guide to enterprise AI infrastructure with open source.
- Take your first steps with MAAS , learning how easy it is to build a fully virtualized sandbox on your laptop in just 30 minutes using Multipass.
Or reach out to our team of experts if you want to learn more about how to get full MAAS support.
As AI platforms grow into large-scale "AI Factories," the real bottleneck shifts from model design to operational complexity. With expensive GPU accelerators, hardware failures and inconsistent configurations lead directly to lost throughput and reduced return on investment. While Kubernetes orchestrates workloads, it cannot fix broken physical infrastructure. This is why bare metal automation is now a first-order AI performance lever. Canonical MAAS is the foundational solution, turning physical servers into programmable, cloud-like resources that can be provisioned, recovered, and repurposed efficiently, ensuring higher utilization and a better ROI for your AI infrastructure.
Categories: AI, AI Factory, bare metal, bare metal kubernetes, MAAS
Source: https://ubuntu.com//blog/the-bare-metal-problem-in-ai-factories Mar 11, 2026, 11:43 PM
#87
Ubuntu Blog / Fast-tracking industrial and ...
Last post by tim - Mar 13, 2026, 06:09 PMFast-tracking industrial and AI deployment on Renesas RZ platforms
Certified Ubuntu 24.04 LTS images now available
Canonical is pleased to announce the general availability (GA) of certified Ubuntu 24.04 LTS and Ubuntu Core 24 images for the Renesas RZ/G2L and RZ/G2LC 64-bit microprocessors (MPUs) platforms. With a production-ready Ubuntu version, users can benefit from enterprise-grade security, long-term support, and full enablement of the rich multimedia capabilities of the Renesas RZ/G series.
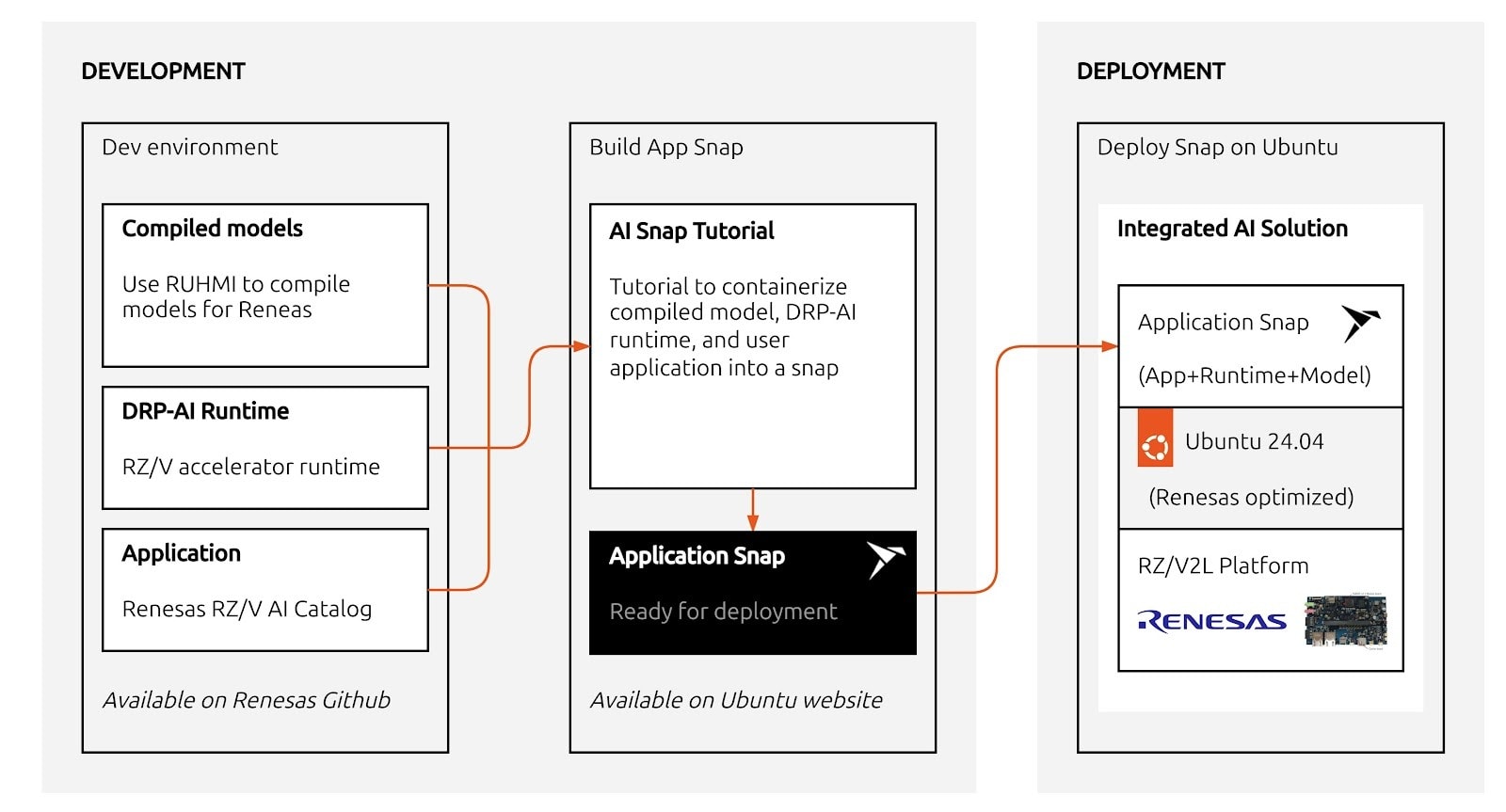
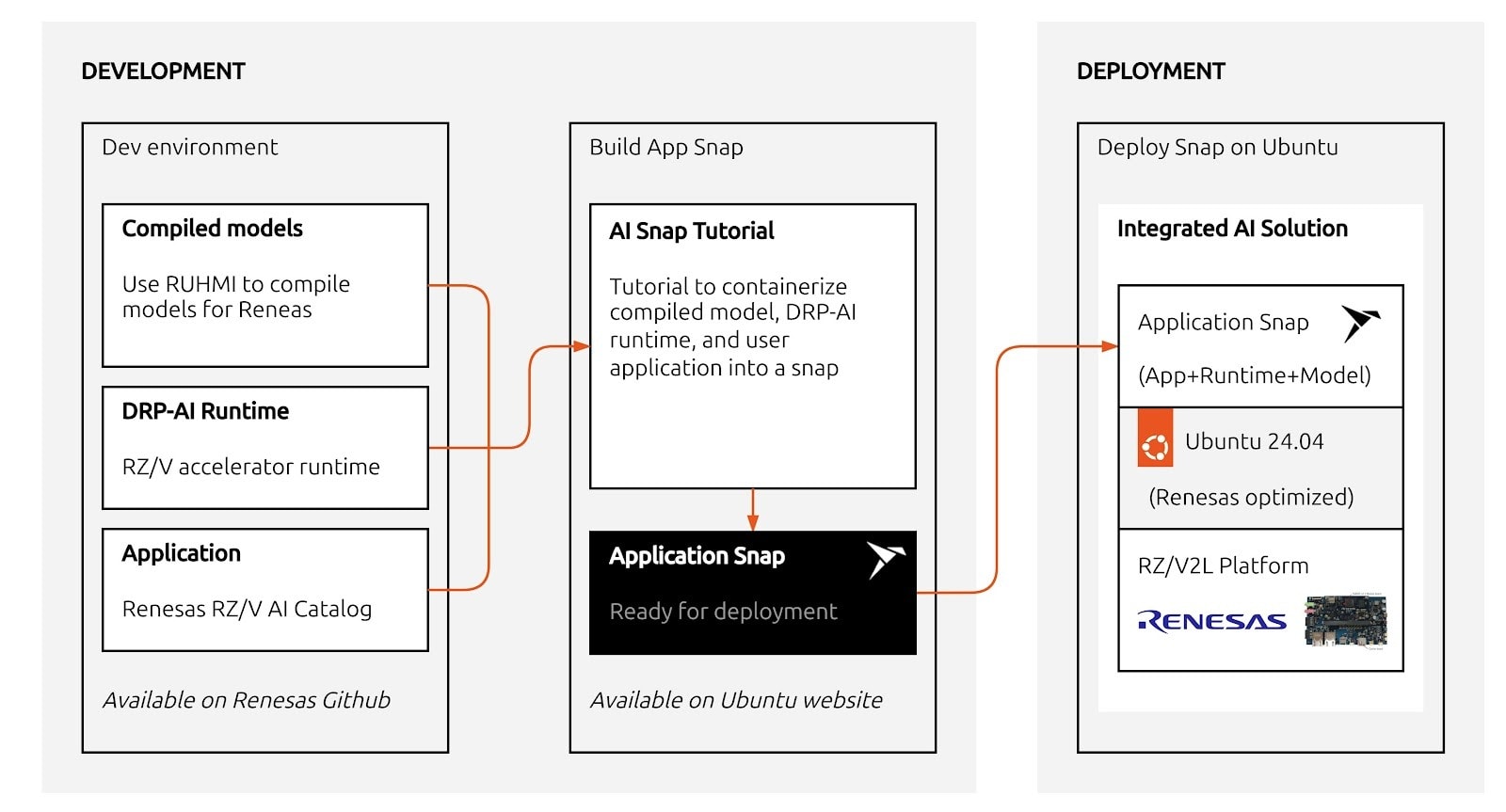
Alongside the GA release for RZ/G2L and RZ/G2LC, Canonical is also introducing an Ubuntu image for the Renesas RZ/V2L platform with an AI snap tutorial to deploy Renesas AI applications on Ubuntu. This image introduces support for Renesas DRP-AI accelerator, enabling high-performance, low-power AI inference at the edge.
Renesas' RZ/G2L and RZ/G2LC groups are general-purpose Arm CortexA55–based MPUs that boost AI performance and extend scalability across entry level to high end designs. They integrate camera inputs, 3D graphics, and video codecs for cost efficient HMI, multimedia and AI image processing applications. The RZ/V2L is optimized for vision AI applications, with the DRP-AI accelerator enabling efficient, real-time AI inference and image processing without an external ISP.
Ubuntu Server and Ubuntu Core: Certified features enablement
The GA Ubuntu 24.04 LTS image is fully certified by Canonical to support the complete feature set of the Renesas RZ/G2L and RZ/G2LC MPUs. This ensures that customers can rely on consistent functionality, performance and stability across production deployments. It also removes the complexity of board bring-up and driver integration, allowing teams to focus on application development rather than platform maintenance.
The certified Ubuntu image is available in both Ubuntu Server and Ubuntu Core variants, allowing customers to select the operating system that best aligns with their product architecture and security requirements. Both variants support Renesas-specific features, including Arm Mali GPU acceleration, Renesas multimedia codec, industrial I/O, and MIPI Camera integration.
Ubuntu Server
Ubuntu Server provides a familiar, flexible Linux environment that is widely adopted across enterprise and embedded deployments. It is the classic, full Ubuntu distribution: headless by default for production, with the flexibility to integrate a graphics stack and UI when required. On Renesas RZ/G2L and RZ/G2LC, Ubuntu Server enables rapid application development, straightforward integration with existing Linux workloads, and access to the full Ubuntu ecosystem of packages and tools.
Ubuntu Core: Security by design
For devices that demand a higher security posture and transactional updates, Ubuntu Core offers a purpose-built, lightweight, immutable operating system optimized for embedded and IoT deployments. On Renesas RZ/G2L and RZ/G2LC, Ubuntu Core enables additional OS features such as:
These capabilities make Ubuntu Core particularly well suited for industrial, smart infrastructure, and mission-critical edge systems.
Meet industrial compliance with Ubuntu Pro
The certified Ubuntu 24.04 LTS image for Renesas RZ/G2L and RZ/G2LC is backed by Canonical's long-term support offering. With an Ubuntu Pro subscription and optional support from Canonical, customers can gain added benefits, including:
Long-term stability is critical for embedded products with extended lifecycles, such as industrial controllers, gateways, and smart edge devices. The need to meet requirements of regulations like the EU Cyber Resilience Act means many organizations are increasingly looking for solutions that prioritize long-term security maintenance and offer support and stability.
Deploying Renesas AI applications on Ubuntu with DRP-AI support
Canonical released an early access Ubuntu 24.04 LTS image for the Renesas RZ/V2L to accelerate AI development and deployment on Ubuntu. This image enables Renesas DRP-AI, a low-power hardware accelerator built for edge Vision AI. DRP-AI offloads vision pre/post-processing and neural network inference from the CPU/GPU to dedicated hardware, delivering predictable real-time performance and higher throughput per watt.
The early access image is accompanied by a hands-on AI snap tutorial that demonstrates how to deploy Renesas AI applications on Ubuntu using the DRP-AI software stack. This lowers friction for teams migrating existing Renesas AI workloads to Ubuntu while preserving performance characteristics and hardware acceleration paths.
"By collaborating with Canonical to bring certified Ubuntu to the RZ/G2L and early access Ubuntu with DRP‑AI on RZ/V2L, we are lowering the barrier to production for edge AI," said Mohammed Dogar, Vice President, Embedded Processing Product Group at Renesas. "Developers can now take Renesas AI applications from prototype to deployment on a secure, long‑term supported Ubuntu platform while fully leveraging DRP‑AI acceleration."
"By collaborating with Renesas, we are jointly ensuring that Ubuntu is ready for production across Renesas RZ platforms," said Cindy Goldberg, VP of Cloud and Silicon Partnerships at Canonical. "Device manufacturers now have a secure, certified platform to deploy with confidence and scale AI solutions from prototype to production."
Deploying Renesas AI applications and reference use cases on Ubuntu streamlines the path from prototype to production. Product teams can evaluate AI workloads for RZ/V2L on Ubuntu ahead of full certification and gain immediate access to Ubuntu's developer ecosystem. By reusing Renesas SDK examples within standard Ubuntu packaging and deployment pipelines, they can enjoy faster time to market.
This early access offering underscores Canonical's commitment to supporting Renesas AI platforms and enabling scalable, secure AI deployments on Ubuntu.
Get started
Download certified Ubuntu images for Renesas RZ/G2L and RZ/G2LC and begin building production-ready solutions with confidence, backed by Canonical's security, certification, and long-term support. Ubuntu Desktop image is available for RZ/G2L for evaluation purposes.
Access RZ/V2L Early access image and AI Snap Tutorial and start evaluating AI workloads on Ubuntu using RZ/V2L DRP-AI accelerator.
For any questions about the platform or further information about Canonical's certification program, contact us .
Certified Ubuntu 24.04 LTS images now available Canonical is pleased to announce the general availability (GA) of certified Ubuntu 24.04 LTS and Ubuntu Core 24 images for the Renesas RZ/G2L and RZ/G2LC 64-bit microprocessors (MPUs) platforms. With a production-ready Ubuntu version, users can benefit from enterprise-grade security, long-term support, and full enablement of the rich [...]
Categories: IoT, Renesas, silicon
Source: https://ubuntu.com//blog/fast-tracking-industrial-and-ai-deployment-on-renesas-rz-platforms Mar 10, 2026, 10:00 AM
Certified Ubuntu 24.04 LTS images now available
Canonical is pleased to announce the general availability (GA) of certified Ubuntu 24.04 LTS and Ubuntu Core 24 images for the Renesas RZ/G2L and RZ/G2LC 64-bit microprocessors (MPUs) platforms. With a production-ready Ubuntu version, users can benefit from enterprise-grade security, long-term support, and full enablement of the rich multimedia capabilities of the Renesas RZ/G series.
Alongside the GA release for RZ/G2L and RZ/G2LC, Canonical is also introducing an Ubuntu image for the Renesas RZ/V2L platform with an AI snap tutorial to deploy Renesas AI applications on Ubuntu. This image introduces support for Renesas DRP-AI accelerator, enabling high-performance, low-power AI inference at the edge.
Renesas' RZ/G2L and RZ/G2LC groups are general-purpose Arm CortexA55–based MPUs that boost AI performance and extend scalability across entry level to high end designs. They integrate camera inputs, 3D graphics, and video codecs for cost efficient HMI, multimedia and AI image processing applications. The RZ/V2L is optimized for vision AI applications, with the DRP-AI accelerator enabling efficient, real-time AI inference and image processing without an external ISP.
Ubuntu Server and Ubuntu Core: Certified features enablement
The GA Ubuntu 24.04 LTS image is fully certified by Canonical to support the complete feature set of the Renesas RZ/G2L and RZ/G2LC MPUs. This ensures that customers can rely on consistent functionality, performance and stability across production deployments. It also removes the complexity of board bring-up and driver integration, allowing teams to focus on application development rather than platform maintenance.
The certified Ubuntu image is available in both Ubuntu Server and Ubuntu Core variants, allowing customers to select the operating system that best aligns with their product architecture and security requirements. Both variants support Renesas-specific features, including Arm Mali GPU acceleration, Renesas multimedia codec, industrial I/O, and MIPI Camera integration.
Ubuntu Server
Ubuntu Server provides a familiar, flexible Linux environment that is widely adopted across enterprise and embedded deployments. It is the classic, full Ubuntu distribution: headless by default for production, with the flexibility to integrate a graphics stack and UI when required. On Renesas RZ/G2L and RZ/G2LC, Ubuntu Server enables rapid application development, straightforward integration with existing Linux workloads, and access to the full Ubuntu ecosystem of packages and tools.
Ubuntu Core: Security by design
For devices that demand a higher security posture and transactional updates, Ubuntu Core offers a purpose-built, lightweight, immutable operating system optimized for embedded and IoT deployments. On Renesas RZ/G2L and RZ/G2LC, Ubuntu Core enables additional OS features such as:
- Full Disk Encryption (FDE) to protect data at rest
- Secure Boot to ensure only trusted software is executed on the device
- Over-the-air updates with automatic rollback
- Application confinement using snap-based packaging
These capabilities make Ubuntu Core particularly well suited for industrial, smart infrastructure, and mission-critical edge systems.
Meet industrial compliance with Ubuntu Pro
The certified Ubuntu 24.04 LTS image for Renesas RZ/G2L and RZ/G2LC is backed by Canonical's long-term support offering. With an Ubuntu Pro subscription and optional support from Canonical, customers can gain added benefits, including:
- Up to 15 years of security maintenance
- Regular CVE fixes for the OS, kernel, and key user-space components
- 24/7 enterprise-grade support from Canonical
Long-term stability is critical for embedded products with extended lifecycles, such as industrial controllers, gateways, and smart edge devices. The need to meet requirements of regulations like the EU Cyber Resilience Act means many organizations are increasingly looking for solutions that prioritize long-term security maintenance and offer support and stability.
Deploying Renesas AI applications on Ubuntu with DRP-AI support
Canonical released an early access Ubuntu 24.04 LTS image for the Renesas RZ/V2L to accelerate AI development and deployment on Ubuntu. This image enables Renesas DRP-AI, a low-power hardware accelerator built for edge Vision AI. DRP-AI offloads vision pre/post-processing and neural network inference from the CPU/GPU to dedicated hardware, delivering predictable real-time performance and higher throughput per watt.
The early access image is accompanied by a hands-on AI snap tutorial that demonstrates how to deploy Renesas AI applications on Ubuntu using the DRP-AI software stack. This lowers friction for teams migrating existing Renesas AI workloads to Ubuntu while preserving performance characteristics and hardware acceleration paths.
"By collaborating with Canonical to bring certified Ubuntu to the RZ/G2L and early access Ubuntu with DRP‑AI on RZ/V2L, we are lowering the barrier to production for edge AI," said Mohammed Dogar, Vice President, Embedded Processing Product Group at Renesas. "Developers can now take Renesas AI applications from prototype to deployment on a secure, long‑term supported Ubuntu platform while fully leveraging DRP‑AI acceleration."
"By collaborating with Renesas, we are jointly ensuring that Ubuntu is ready for production across Renesas RZ platforms," said Cindy Goldberg, VP of Cloud and Silicon Partnerships at Canonical. "Device manufacturers now have a secure, certified platform to deploy with confidence and scale AI solutions from prototype to production."
Deploying Renesas AI applications and reference use cases on Ubuntu streamlines the path from prototype to production. Product teams can evaluate AI workloads for RZ/V2L on Ubuntu ahead of full certification and gain immediate access to Ubuntu's developer ecosystem. By reusing Renesas SDK examples within standard Ubuntu packaging and deployment pipelines, they can enjoy faster time to market.
This early access offering underscores Canonical's commitment to supporting Renesas AI platforms and enabling scalable, secure AI deployments on Ubuntu.
Get started
Download certified Ubuntu images for Renesas RZ/G2L and RZ/G2LC and begin building production-ready solutions with confidence, backed by Canonical's security, certification, and long-term support. Ubuntu Desktop image is available for RZ/G2L for evaluation purposes.
Access RZ/V2L Early access image and AI Snap Tutorial and start evaluating AI workloads on Ubuntu using RZ/V2L DRP-AI accelerator.
For any questions about the platform or further information about Canonical's certification program, contact us .
Certified Ubuntu 24.04 LTS images now available Canonical is pleased to announce the general availability (GA) of certified Ubuntu 24.04 LTS and Ubuntu Core 24 images for the Renesas RZ/G2L and RZ/G2LC 64-bit microprocessors (MPUs) platforms. With a production-ready Ubuntu version, users can benefit from enterprise-grade security, long-term support, and full enablement of the rich [...]
Categories: IoT, Renesas, silicon
Source: https://ubuntu.com//blog/fast-tracking-industrial-and-ai-deployment-on-renesas-rz-platforms Mar 10, 2026, 10:00 AM
#88
Ubuntu Blog / Canonical and Arduino collabo...
Last post by tim - Mar 13, 2026, 06:09 PMCanonical and Arduino collaborate to enable Ubuntu on the VENTUNO Q, the next generation platform for AI
Through a strategic partnership with Canonical, Arduino's latest product offers a seamless Linux experience for complex AI workloads in robotics, edge AI vision and more.
LONDON, UK – March 9, 2026 – Today, Arduino announced the launch of the Arduino® VENTUNO™ Q, a dual-brain board designed for high-performance computing and physical actuation. VENTUNO Q represents a significant step in the Arduino-Qualcomm Technologies, Inc.-Canonical collaboration, embracing a developer-first philosophy with Ubuntu.
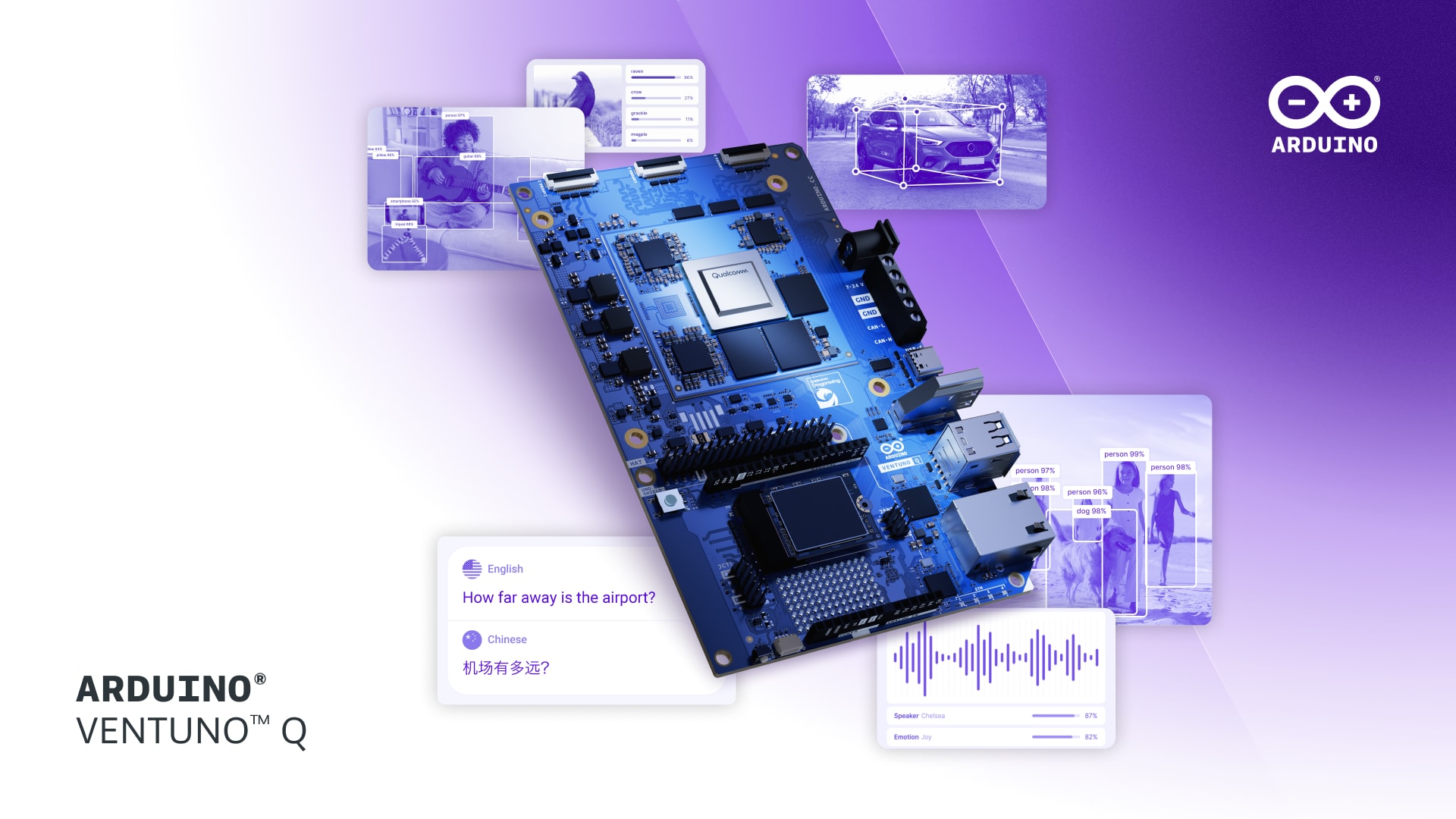
Dual-brain architecture: Intelligence meets reflexes
VENTUNO Q introduces a high-performance dual-brain architecture, engineered for machines that must move as fast as they think. Powered by the Qualcomm Dragonwing™ IQ-8275 processor, the board brings 40 dense TOPS of industrial-grade AI compute to a compact form factor. This allows for the local execution of Large Language Models (LLMs), Visual Language Models (VLMs), and high-throughput computer vision entirely at the edge. Ubuntu runs natively on this primary processor providing the core development and inference environment.
A dedicated STM32H5 microcontroller ensures sub-millisecond, deterministic control for motors and sensors. This allows AI-driven decisions to be translated into physical action instantly, without the latency associated with traditional single-processor systems.
Ubuntu for instant innovation
To ensure a frictionless out-of-the-box experience, the VENTUNO Q arrives with Ubuntu. This enables developers to go from unboxing to AI inference in minutes, eliminating the traditional hurdles of complex board support packages (BSPs) and fragmented kernel drivers.
Running natively on top of Ubuntu is the Arduino® App Lab. This unified, collaborative environment allows developers to blend Arduino sketches, Python scripts, and advanced AI Bricks into ready-to-deploy applications. Whether in Standalone Mode, connected directly to a monitor, or PC-Connected Mode, the Arduino App Lab provides a smooth path for both hobbyists and R&D engineers to master the Qualcomm AI stack.
The prototyping-to-production pipeline
While optimized for the Arduino DIY maker market, the VENTUNO Q is built with industrial-grade specs. By integrating the IQ-8275 with Ubuntu, it offers a seamless path for developers to transition their prototypes directly into production-ready industrial applications.
"Arduino VENTUNO Q is the definitive powerhouse for AI and robotics," said Fabio Violante, Vice President and General Manager of Arduino at Qualcomm. "By merging high-performance AI capabilities with their direct, real-time application in actuation, we are empowering creators to build systems that interact with the world. With Ubuntu and the Arduino App Lab experience, we are delivering the most flexible edge AI ecosystem ever built."
"Our collaboration with Arduino and Qualcomm provides a production-ready starting line for innovators," said Cindy Goldberg, VP of Silicon Alliances at Canonical. "By providing a reliable Ubuntu foundation for VENTUNO Q, we ensure that a successful prototype can scale into a securely-designed industrial solution with 10 years of security maintenance."
Availability
Arduino VENTUNO Q will be available for open sale soon. Developers can get a first look at the Ubuntu powered platform and new Arduino App Lab models at Embedded World 2026. Contact us to schedule a meeting at the event. Visit the official page atarduino.cc/product-ventuno-q to sign up for notifications and be the first to know when the product is available.
To find out more about the Canonical and Qualcomm partnership, check out our video:
About Arduino
Arduino (a Qualcomm Technologies, Inc. company) is a leading open-source hardware and software provider and an accessible platform for creating interactive projects. With an estimated 33 million active users, the Arduino ecosystem has expanded over 20 years to address new demands and challenges, offering products for IoT, wearables, 3D printing, and embedded environments.
About Canonical
Canonical, the publisher of Ubuntu, provides open source security, support and services. Our portfolio covers critical systems, from the smallest devices to the largest clouds, from the kernel to containers, from databases to AI. With customers that include top tech brands, emerging startups, governments and home users, Canonical delivers trusted open source for everyone.
Learn more at https://canonical.com/
Qualcomm branded products are products of Qualcomm Technologies, Inc. and/or its subsidiaries. Arduino, VENTUNO, UNO, and Modulino are trademarks or registered trademarks of Arduino S.r.l.
Through a strategic partnership with Canonical, Arduino's latest product offers a seamless Linux experience for complex AI workloads in robotics, edge AI vision and more. LONDON, UK – March 9, 2026 – Today, Arduino announced the launch of the Arduino® VENTUNO™ Q, a dual-brain board designed for high-performance computing and physical actuation. VENTUNO Q represents [...]
Categories: hardware enablement, qualcomm
Source: https://ubuntu.com//blog/canonical-and-arduino-collaborate-to-enable-ubuntu-on-the-ventuno-q-the-next-generation-platform-for-ai Mar 09, 2026, 06:02 PM
Through a strategic partnership with Canonical, Arduino's latest product offers a seamless Linux experience for complex AI workloads in robotics, edge AI vision and more.
LONDON, UK – March 9, 2026 – Today, Arduino announced the launch of the Arduino® VENTUNO™ Q, a dual-brain board designed for high-performance computing and physical actuation. VENTUNO Q represents a significant step in the Arduino-Qualcomm Technologies, Inc.-Canonical collaboration, embracing a developer-first philosophy with Ubuntu.
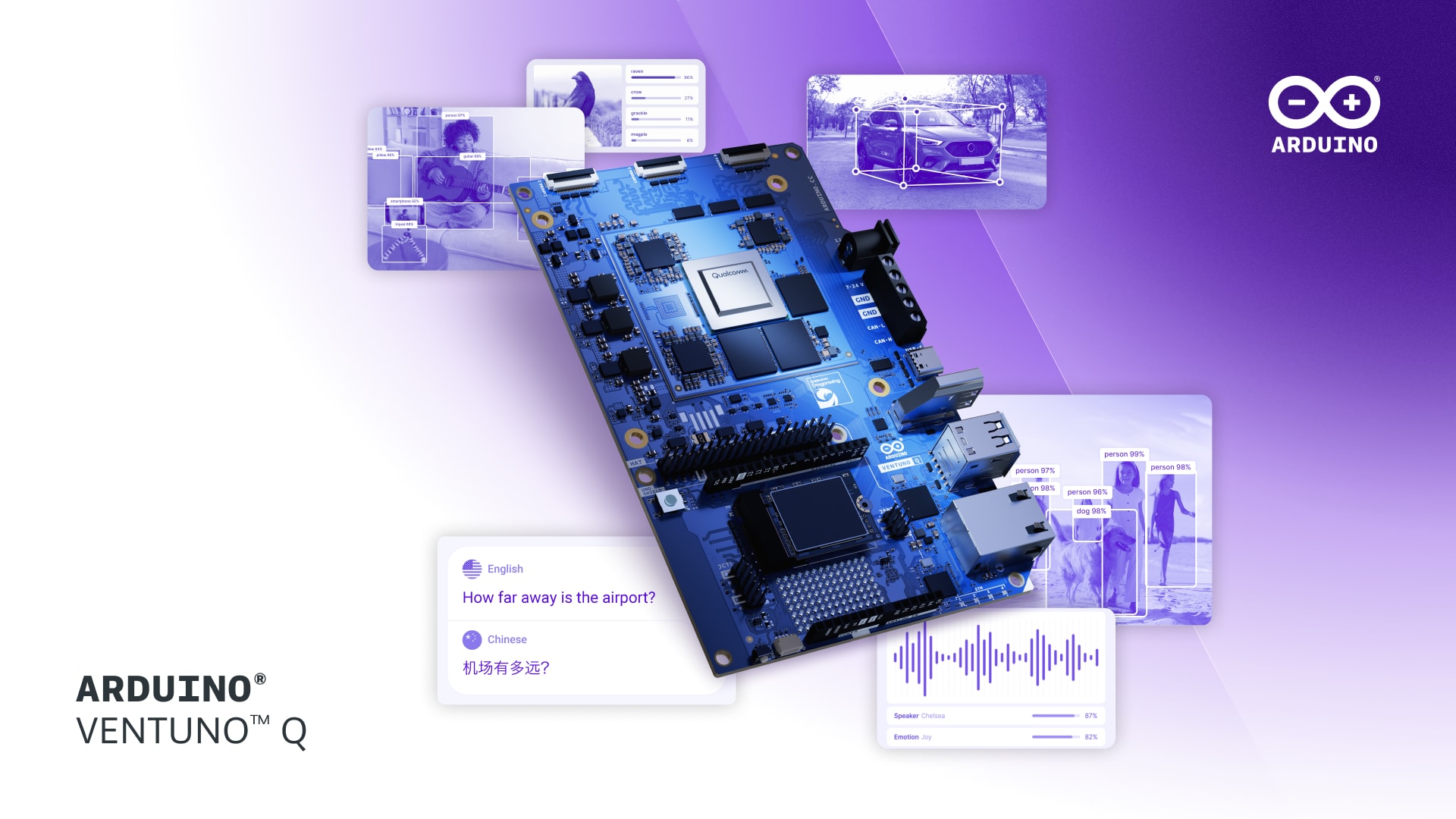
Dual-brain architecture: Intelligence meets reflexes
VENTUNO Q introduces a high-performance dual-brain architecture, engineered for machines that must move as fast as they think. Powered by the Qualcomm Dragonwing™ IQ-8275 processor, the board brings 40 dense TOPS of industrial-grade AI compute to a compact form factor. This allows for the local execution of Large Language Models (LLMs), Visual Language Models (VLMs), and high-throughput computer vision entirely at the edge. Ubuntu runs natively on this primary processor providing the core development and inference environment.
A dedicated STM32H5 microcontroller ensures sub-millisecond, deterministic control for motors and sensors. This allows AI-driven decisions to be translated into physical action instantly, without the latency associated with traditional single-processor systems.
Ubuntu for instant innovation
To ensure a frictionless out-of-the-box experience, the VENTUNO Q arrives with Ubuntu. This enables developers to go from unboxing to AI inference in minutes, eliminating the traditional hurdles of complex board support packages (BSPs) and fragmented kernel drivers.
Running natively on top of Ubuntu is the Arduino® App Lab. This unified, collaborative environment allows developers to blend Arduino sketches, Python scripts, and advanced AI Bricks into ready-to-deploy applications. Whether in Standalone Mode, connected directly to a monitor, or PC-Connected Mode, the Arduino App Lab provides a smooth path for both hobbyists and R&D engineers to master the Qualcomm AI stack.
The prototyping-to-production pipeline
While optimized for the Arduino DIY maker market, the VENTUNO Q is built with industrial-grade specs. By integrating the IQ-8275 with Ubuntu, it offers a seamless path for developers to transition their prototypes directly into production-ready industrial applications.
"Arduino VENTUNO Q is the definitive powerhouse for AI and robotics," said Fabio Violante, Vice President and General Manager of Arduino at Qualcomm. "By merging high-performance AI capabilities with their direct, real-time application in actuation, we are empowering creators to build systems that interact with the world. With Ubuntu and the Arduino App Lab experience, we are delivering the most flexible edge AI ecosystem ever built."
"Our collaboration with Arduino and Qualcomm provides a production-ready starting line for innovators," said Cindy Goldberg, VP of Silicon Alliances at Canonical. "By providing a reliable Ubuntu foundation for VENTUNO Q, we ensure that a successful prototype can scale into a securely-designed industrial solution with 10 years of security maintenance."
Availability
Arduino VENTUNO Q will be available for open sale soon. Developers can get a first look at the Ubuntu powered platform and new Arduino App Lab models at Embedded World 2026. Contact us to schedule a meeting at the event. Visit the official page atarduino.cc/product-ventuno-q to sign up for notifications and be the first to know when the product is available.
To find out more about the Canonical and Qualcomm partnership, check out our video:
About Arduino
Arduino (a Qualcomm Technologies, Inc. company) is a leading open-source hardware and software provider and an accessible platform for creating interactive projects. With an estimated 33 million active users, the Arduino ecosystem has expanded over 20 years to address new demands and challenges, offering products for IoT, wearables, 3D printing, and embedded environments.
About Canonical
Canonical, the publisher of Ubuntu, provides open source security, support and services. Our portfolio covers critical systems, from the smallest devices to the largest clouds, from the kernel to containers, from databases to AI. With customers that include top tech brands, emerging startups, governments and home users, Canonical delivers trusted open source for everyone.
Learn more at https://canonical.com/
Qualcomm branded products are products of Qualcomm Technologies, Inc. and/or its subsidiaries. Arduino, VENTUNO, UNO, and Modulino are trademarks or registered trademarks of Arduino S.r.l.
Through a strategic partnership with Canonical, Arduino's latest product offers a seamless Linux experience for complex AI workloads in robotics, edge AI vision and more. LONDON, UK – March 9, 2026 – Today, Arduino announced the launch of the Arduino® VENTUNO™ Q, a dual-brain board designed for high-performance computing and physical actuation. VENTUNO Q represents [...]
Categories: hardware enablement, qualcomm
Source: https://ubuntu.com//blog/canonical-and-arduino-collaborate-to-enable-ubuntu-on-the-ventuno-q-the-next-generation-platform-for-ai Mar 09, 2026, 06:02 PM
#89
Ubuntu News / Google Chrome is (finally) co...
Last post by tim - Mar 13, 2026, 06:09 PMGoogle Chrome is (finally) coming to ARM64 Linux
 Chrome is finally coming to ARM64 Linux devices this year, Google has announced. If you currently run Ubuntu (or another Linux distribution) on an ARM-based device like the Raspberry Pi or a Snapdragon X Elite laptop, etc, you've had no way to install an official Google Chrome build, only Chromium, the open-source project on which Chrome is based. The lack of an official Google Chrome ARM build for Linux has always been puzzling given that Chromium supports ARM, and lots of Chromebooks are ARM-based. Today (12 March, 2026) the confusion can end. The search giant says its proprietary browser will [...]
Chrome is finally coming to ARM64 Linux devices this year, Google has announced. If you currently run Ubuntu (or another Linux distribution) on an ARM-based device like the Raspberry Pi or a Snapdragon X Elite laptop, etc, you've had no way to install an official Google Chrome build, only Chromium, the open-source project on which Chrome is based. The lack of an official Google Chrome ARM build for Linux has always been puzzling given that Chromium supports ARM, and lots of Chromebooks are ARM-based. Today (12 March, 2026) the confusion can end. The search giant says its proprietary browser will [...]
You're reading Google Chrome is (finally) coming to ARM64 Linux , a blog post from OMG! Ubuntu . Do not reproduce elsewhere without permission.
Categories: News, App Updates, arm, Google, Google Chrome
Source: https://www.omgubuntu.co.uk/2026/03/google-chrome-arm64-linux Mar 13, 2026, 02:07 AM
 Chrome is finally coming to ARM64 Linux devices this year, Google has announced. If you currently run Ubuntu (or another Linux distribution) on an ARM-based device like the Raspberry Pi or a Snapdragon X Elite laptop, etc, you've had no way to install an official Google Chrome build, only Chromium, the open-source project on which Chrome is based. The lack of an official Google Chrome ARM build for Linux has always been puzzling given that Chromium supports ARM, and lots of Chromebooks are ARM-based. Today (12 March, 2026) the confusion can end. The search giant says its proprietary browser will [...]
Chrome is finally coming to ARM64 Linux devices this year, Google has announced. If you currently run Ubuntu (or another Linux distribution) on an ARM-based device like the Raspberry Pi or a Snapdragon X Elite laptop, etc, you've had no way to install an official Google Chrome build, only Chromium, the open-source project on which Chrome is based. The lack of an official Google Chrome ARM build for Linux has always been puzzling given that Chromium supports ARM, and lots of Chromebooks are ARM-based. Today (12 March, 2026) the confusion can end. The search giant says its proprietary browser will [...]You're reading Google Chrome is (finally) coming to ARM64 Linux , a blog post from OMG! Ubuntu . Do not reproduce elsewhere without permission.
Categories: News, App Updates, arm, Google, Google Chrome
Source: https://www.omgubuntu.co.uk/2026/03/google-chrome-arm64-linux Mar 13, 2026, 02:07 AM
#90
Ubuntu News / I tried Firefox’s new AI ‘Sma...
Last post by tim - Mar 13, 2026, 06:09 PMI tried Firefox's new AI 'Smart Window' in a beta build
 Firefox's new AI-powered 'Smart Window' feature is taking shape in development builds – I gave it a hands on in the latest v149.0b7 beta (on macOS). Although Firefox 148 added an AI Switch, Mozilla is all-in on AI in now it's part of its double-bottom line and a way to generate money. Firefox's upcoming Smart Window is key to this, as it makes AI the primary interface for browsing. What follows is a hands-on with Smart Window in Firefox 149 beta, how it works, how it's activated and why its 'memory' feature gave me the ick. Firefox's new Smart Window [...]
Firefox's new AI-powered 'Smart Window' feature is taking shape in development builds – I gave it a hands on in the latest v149.0b7 beta (on macOS). Although Firefox 148 added an AI Switch, Mozilla is all-in on AI in now it's part of its double-bottom line and a way to generate money. Firefox's upcoming Smart Window is key to this, as it makes AI the primary interface for browsing. What follows is a hands-on with Smart Window in Firefox 149 beta, how it works, how it's activated and why its 'memory' feature gave me the ick. Firefox's new Smart Window [...]
You're reading I tried Firefox's new AI 'Smart Window' in a beta build , a blog post from OMG! Ubuntu . Do not reproduce elsewhere without permission.
Categories: News, AI/ML, Firefox, Mozilla
Source: https://www.omgubuntu.co.uk/2026/03/firefox-smart-window-hands-on Mar 12, 2026, 05:23 AM
 Firefox's new AI-powered 'Smart Window' feature is taking shape in development builds – I gave it a hands on in the latest v149.0b7 beta (on macOS). Although Firefox 148 added an AI Switch, Mozilla is all-in on AI in now it's part of its double-bottom line and a way to generate money. Firefox's upcoming Smart Window is key to this, as it makes AI the primary interface for browsing. What follows is a hands-on with Smart Window in Firefox 149 beta, how it works, how it's activated and why its 'memory' feature gave me the ick. Firefox's new Smart Window [...]
Firefox's new AI-powered 'Smart Window' feature is taking shape in development builds – I gave it a hands on in the latest v149.0b7 beta (on macOS). Although Firefox 148 added an AI Switch, Mozilla is all-in on AI in now it's part of its double-bottom line and a way to generate money. Firefox's upcoming Smart Window is key to this, as it makes AI the primary interface for browsing. What follows is a hands-on with Smart Window in Firefox 149 beta, how it works, how it's activated and why its 'memory' feature gave me the ick. Firefox's new Smart Window [...]You're reading I tried Firefox's new AI 'Smart Window' in a beta build , a blog post from OMG! Ubuntu . Do not reproduce elsewhere without permission.
Categories: News, AI/ML, Firefox, Mozilla
Source: https://www.omgubuntu.co.uk/2026/03/firefox-smart-window-hands-on Mar 12, 2026, 05:23 AM